Forensic investigations are always challenging as you may gather all the information you could for the evidence and mitigation plan. Here are some of the computer forensic investigator tools you would need. Most of them are free!
Whether it’s for an internal human resources case, an investigation into unauthorized access to a server, or if you just want to learn a new skill, these suites and utilities will help you conduct memory forensic analysis, hard drive forensic analysis, forensic image exploration, forensic imaging and mobile forensics. As such, they all provide the ability to bring back in-depth information about what’s “under the hood” of a system.
1. Autopsy
Autopsy is a GUI-based open source digital forensic program to analyze hard drives and smart phones effectively. Autospy is used by thousands of users worldwide to investigate what actually happened in the computer.
2. Encrypted Disk Detector
Encrypted Disk Detector can be helpful to check encrypted physical drives. It supports TrueCrypt, PGP, Bitlocker, Safeboot encrypted volumes.
3. Wireshark
Wireshark is a network capture and analyzer tool to see what’s happening in your network. Wireshark will be handy to investigate network related incident.
4. Magnet RAM Capture
You can use Magnet RAM capture to capture the physical memory of a computer and analyze artifacts in memory.
It supports Windows operating system.
5. Network Miner
An interesting network forensic analyzer for Windows, Linux & MAC OS X to detect OS, hostname, sessions and open ports through packet sniffing or by PCAP file. Network Miner provide extracted artifacts in an intuitive user interface.
6. NMAP
NMAP (Network Mapper) is one of the most popular networks and security auditing tools. NMAP is supported on most of the operating systems including Windows, Linux, Solaris, MAC OS, HP-UX etc. It’s open source so free.
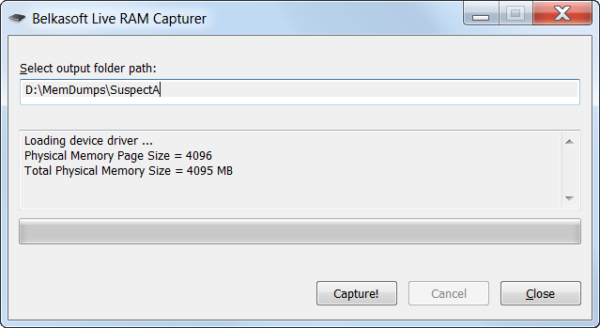
7. RAM Capturer
RAM Capturer by Belkasoft is a free tool to dump the data from computer’s volatile memory. It’s compatible with Windows OS. Memory dumps may contain encrypted volume’s password and login credentials for webmails and social network services.
8. Forensic Investigator
If you are using Splunk then Forensic Investigator will be a very handy tool. It’s Splunk app and has many tools combined.
9. FAW
FAW (Forensics Acquisition of Websites) is to acquire web pages for forensic investigation which has the following features.
- Capture the entire or partial page
- Capture all types of image
- Capture HTML source code of the web page
- Integrate with Wireshark
10. HashMyFiles
HashMyFiles will help you to calculate the MD5 and SHA1 hashes. It works on almost all latest Windows OS.
11. USB Write Blocker
View the USB drives content without leaving the fingerprint, changes to metadata and timestamps. USB Write Blocker use Windows registry to write-block USB devices.
12. Crowd Response
Response by Crowd Strike is a windows application to gather system information for incident response and security engagements. You can view the results in XML, CSV, TSV or HTML with help of CRConvert. It runs on 32 or 64 bit of Windows XP above.
Crowd Strike has some other nice tools for investigation.
- Totrtilla – anonymously route TCP/IP and DNS traffic through TOR.
- Shellshock Scanner – scan your network for shellshock vulnerability
- Heartbleed scanner – scan your network for OpenSSL heart bleed vulnerability
13. NFI Defraser
Defraser forensic tool may help you to detect full and partial multimedia files in the data streams.
14. ExifTool
ExifTool helps you to read, write and edit meta information for a number of file types. It can read EXIF, GPS, IPTC, XMP, JFIF, GeoTIFF, Photoshop IRB, FlashPix, etc.
15. Toolsley
Toolsley got more than 10 useful tools for investigation.
- File signature verifier
- File identifier
- Hash & Validate
- Binary inspector
- Encode text
- Data URI generator
- Password generator
16. SIFT
SIFT (SANS investigative forensic toolkit) workstation is freely available as Ubuntu 14.04. SIFT is a suite of forensic tools you need and one of the most popular open source incident response platform.
17. Dumpzilla
Extract all interesting information from Firefox, Iceweasel and Seamonkey browser to be analyzed with Dumpzilla.
18. Browser History
Foxton has two free interesting tools.
- Browser history capturer – capture web browser (chrome, firefox, IE & edge) history on Windows OS.
- Browser history viewer – extract ana analyze internet activity history from most of the modern browsers. Results are shown in the interactive graph and historical data can be filtered.
19. ForensicUserInfo
Extract the following information with ForensicUserInfo.
- RID
- LM/NT Hash
- Password reset/Account expiry date
- Login count/fail date
- Groups
- Profile path
20. Kali Linux
Kali Linux is one of the most popular platforms for penetration testing but it has forensic capability too.
21. Paladin
PALADIN forensic suite – the world’s most popular Linux forensic suite is a modified Linux distro based on Ubuntu available in 32 and 64 bit.
22. Sleuth Kit
The Sleuth Kit is a collection of command line tools to investigate and analyze volume and file systems to find the evidence.
23. CAINE
CAINE (Computer Aided Investigate Environment) is Linux distro that offers the complete forensic platform which has more than 80 tools for you to analyze, investigate and create an actionable report.
24. Volatility
Volatility is the memory forensics framework. It used for incident response and malware analysis. With this tool, you can extract information from running processes, network sockets, network connection, DLLs and registry hives. It also has support for extracting information from Windows crash dump files and hibernation files. This tool is available for free under GPL license.
25. WindowSCOPE
WindowsSCOPE is another memory forensics and reverse engineering tool used for analyzing volatile memory. It is basically used for reverse engineering of malwares. It provides the capability of analyzing the Windows kernel, drivers, DLLs, virtual and physical memory.
26. The Coroner’s Toolkit
The Coroner’s Toolkit or TCT is also a good digital forensic analysis tool. It runs under several Unix-related operating systems. It can be used to aid analysis of computer disasters and data recovery.
27. Bulk Extractor
Bulk Extractor is also an important and popular digital forensics tool. It scans the disk images, file or directory of files to extract useful information. In this process, it ignores the file system structure, so it is faster than other available similar kinds of tools. It is basically used by intelligence and law enforcement agencies in solving cyber crimes.
28. Oxygen Forensic Suite
If you are investigating a case that requires you to gather evidence from a mobile phone to support your case, Oxygen Forensics Suite (Standard Edition) is a tool that will help you achieve this.
29. Free Hex Editor Neo
Free Hex Editor Neo is a basic hex editor that was designed to handle very large files. While a lot of the additional features are found in the commercial versions of Hex Editor Neo, I find this tool useful for loading large files (e.g. database files or forensic images) and performing actions such as manual data carving, low-level file editing, information gathering, or searching for hidden data.
30. Xplico
Xplico is an open source Network Forensic Analysis Tool (NFAT) that aims to extract applications data from internet traffic (e.g. Xplico can extract an e-mail message from POP, IMAP or SMTP traffic). Features include support for a multitude of protocols (e.g. HTTP, SIP, IMAP, TCP, UDP), TCP reassembly, and the ability to output data to a MySQL or SQLite database, amongst others.