Digital Forensics & Cyber Security Blog
Digital Forensics & Cyber Security Blog
Exporting your data from Google
Exporting your data from Google It’s no secret that Google collects immense amounts of data from its users every day. Locations, photos, messages and more, it’s all in the cloud. Ever wonder what they have on you? Fortunately Google makes it easy to [...]
923 words on Windows NTUSER.dat
LIFARS Technical Guide In this article we will be focusing only on NTUSER.DAT and not on related registry hives or artifacts that are not located within NTUSER hive. This file which stores user profile and settings information can be useful in many use cases. We can gain evidence of program [...]
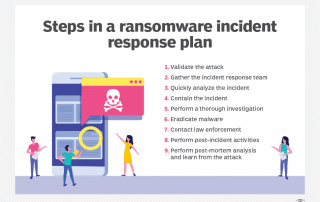
9-step ransomware incident response plan
Ransomware is no longer just an endpoint being encrypted by malware. Servers, applications and even data stored in cloud services can be encrypted and held for ransom. While the specific recommendations vary depending on the systems involved in an incident, being prepared with a comprehensive plan can help reduce the [...]
Best Ways to Sanitize and Kill the Viruses Living on Your iPhone
Whether it’s keeping the screen pristine or regularly cleaning out ports, most iPhone owners do their part to keep their device in good shape. But how can an iPhone affect your own physical health? With recent attention turning to cleanliness as a high-priority concern, there are now more reasons than [...]
Do you want a coffee?
Did you know you are being followed everywhere you go? Cell Phone providers constantly ping your phone and smart devices to see where you are. They hope they can reach you, their customers based on where you are or have been to direct you to new purchases. Some say where [...]
The ever-changing landscape for digital forensic tools…
In the ever-changing world of digital and mobile device forensics we are still seeing new technologies and tools being introduced around the world. There will be several new tools announced in the coming months. Perhaps at currently scheduled events… or maybe just a virtual summit to engage and enthuse digital [...]
How Far Would You Go to Get Your Kid Off Their Phone? This Dad Took His Son From Canada to Mongolia
How do you get a teen to put down their phone and talk to you? If you're Jamie Clarke you invite your kid on a month long trip to Mongolia. Riding through a remote valley in Mongolia on the back of his motorbike, adventurer Jamie Clarke let the hum of [...]
Emoji Forensics
Emojis are everywhere - and that includes your evidence. What is an emoji? It is a small digital image or icon used to express and idea or an emotion. They are much like emoticons, but emoji are actual pictures instead of typographics. Originally meaning pictograph, the word emoji comes from Japanese (絵, "picture") + moji (文字, "character"); the [...]
Windows 10 Vulnerability
On January 14th, the National Security Agency (NSA) Cybersecurity Directorate head Anne Neuberger announced a critical Windows 10 bug that could have led more than 900 million PCs vulnerable to attack. On the same day, Microsoft immediately released a patch for Windows 10 and Server 2016 after NSA disclosed this vulnerability. Through [...]
12 Things You Should Have Done to Stop Ransomware
Here is a list of 12 things you should be doing to stop ransomware from killing your business. 1. Application Whitelisting Most employees use between 5-10 applications to perform their job functions. With that in mind, operating systems are pretty much left wide open, so any application, malicious or otherwise, [...]