We wanted to share some useful tips from our friends at BlackBag:
While the amounts of data in typical digital forensic cases today is a lot different than it was several years ago, the amount of time most investigators have to do their analysis has not changed.
Below are 7 strategies that will help investigators save time and be the most effective in their analysis.
1. MAKE A PLAN
When an investigator first gets a case, there are a few questions they answer at the start:
- What are the case objectives?
- What information do I know about the evidence?
- What are the OS’s and filesystems?
- What are the constraints?
Most of the these questions can be determined while the digital evidence is being processed. By knowing the background of the case and the type of filesystem up front, once processing is complete the investigator can go straight to the areas of interest.
2. KNOW YOUR TOOL
There are a lot of digital forensic analysis tools on the market today and they all perform very differently. Knowing how long certain functions take to process in your tool of choice, as well as what the minimum requirements are to process a case can go a long way in prioritizing what gets done first. Some investigators are against using checklists because they feel it doesn’t allow them to think outside of the box if they need to. However, having a list of go-to artifacts and where they are located can help speed up the analysis. If the tool allows, save templates for different case types so you don’t have recreate the wheel every time you start a new case. Also never be afraid to reach out to the tool developers. If something isn’t working as well or as fast as you think it should, definitely let them know. Most developers love to prioritize user specific requirements over nice to haves.
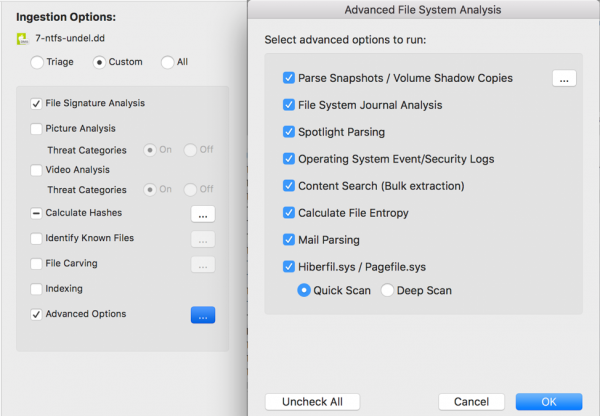
Blacklight has a lot of processing options, as seen in the below picture. Most of the items do not have to be selected at the start of the case. Some processes, such has ‘Calculate File Entropy’ take a long time to run. When processing cases where no encrypted is expected, you can uncheck it. If signs of encryption are encountered during the analysis, go back and run that function at that time.
Another timesaving advantage of BlackLight is most of the areas needing review can be reviewed in BlackLight. Data can be processed one time with BlackLight providing disk view, memory analysis, registry analysis, plist viewing, and database viewing.
3. LIMIT SCOPE WHERE APPROPRIATE
While making the analysis plan based on case information, the investigator should already have an idea of areas to target first. Analysis may focus on specific locations (user directories, applications, etc.), files altered during a specific time range, or possibly files by file size. Filtering and hash sets can also help narrow the scope by removing files that wouldn’t be of interest, for example operating system files. Once the investigator has the scope narrowed down, the use of tags/bookmarks can help keep things organized from the start and limit the time needed to go back to files already reviewed.
4. DECREASE NUMBER OF PICTURES AND VIDEOS TO REVIEW
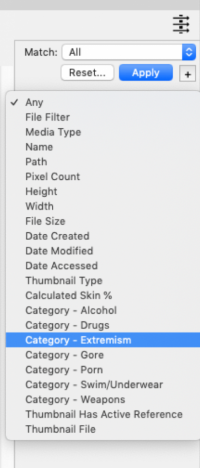
Starting with Blacklight 2019 R1, Image Analyzer has been integrated and can help narrow down images based on threat categories. There are several categories built in to the program that can be used in filters. Categories to date include Porn, Drugs, Extremism, Gore, Alcohol, Swimwear/Underwear, and Weapons.
5. USE SEARCH STRATEGIES
There are three main types of searches in BlackLight. First, raw searching can do string searches against the image as a whole, or selected portions of the image. There is no up-front processing needed but individual searches can take a long time depending on the size of the image. Second, regular expressions look for specific patterns of data, such as phone numbers or email addresses. Like a raw search, regular expressions can be run as needed. Pre-configured regular expressions can be run against memory files at any point during analysis. Lastly, smart indexing has been added to BlackLight since release 2019 R1. Indexing looks for whole words or terms, and smart indexing focuses on the files containing words and metadata. As of the time of this writing, indexing is currently being done against allocated files. Building the index takes time, but once complete searching the index is really quick.
6. ACCESS AND ASSESS HIGH LEVEL INFO QUICKLY
BlackLight’s reporting capability makes it easy to quickly export reports. As soon as the data is processed a report can be generated based on what has been processed. Communication, Actionable Intel, Locations, etc. can be readily exported to hand off critical info to other analysts that may need it. This can be especially useful with mobile devices.
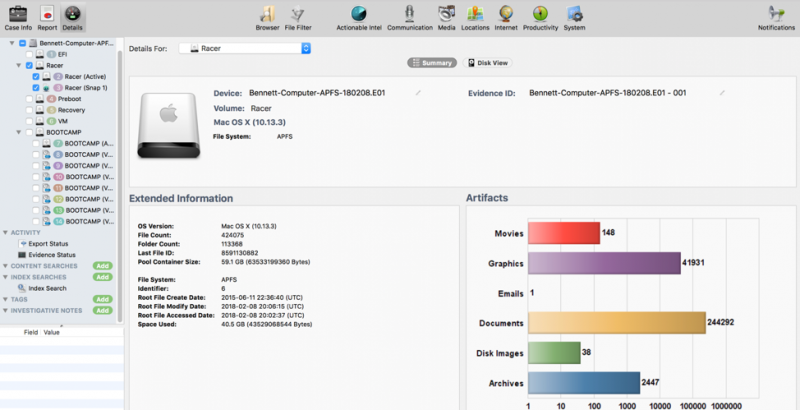
Another way to see high level info quickly is the Summary tab within Blacklight. Once data has been processed, this screen will show what operating system is installed, how many files there are, and file counts based on the type of file (movies, graphics, email, etc).
7. PRIORITIZE ANALYSIS
Many cases have multiple devices. The processing of each item has to be prioritized. BlackLight’s ability to provide high level info quickly, which can then be used to determine which device(s) to examine first.
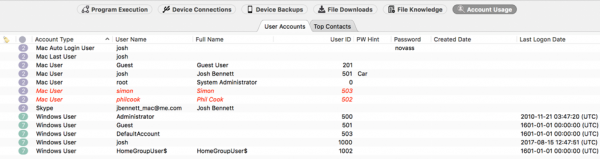
Account Usage in BlackLight helps prioritize by showing who the current users of the system are, as well as any deleted users that may have previously used the device.
SUMMARY
In summary, data sets aren’t getting any smaller. Investigators need to use information to strategize prior to loading and processing everything in a case. Know your tool and how it handles a large number of devices. Where possible, use the tool to help you discover where the best places to start are for specific types of investigations. BlackLight provides investigative leads and actionable intelligence, use it. Use filtering, tagging, searching techniques, and extracted data sets to narrow your focus. Finally, make a plan of approach for each type of case, but remain flexible.